Cybercrime poses a significant threat to businesses in South Africa, with many companies falling victim to data breaches, ransomware attacks, and phishing scams. As reliance on digital platforms increases, protecting your business from cyber threats has become more critical than ever.
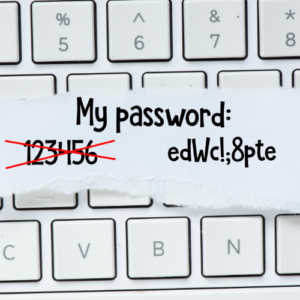
One of the first steps in enhancing cybersecurity is implementing strong password policies. Encourage employees to use complex passwords that include a mix of letters, numbers, and symbols, and mandate regular password changes. Enabling two-factor authentication (2FA) adds an extra layer of security, making it more difficult for unauthorized users to gain access to sensitive information.
Regular software updates are another essential component of a robust cybersecurity strategy. Software developers frequently release patches to address vulnerabilities that cybercriminals can exploit. By keeping all systems and software updated, businesses can significantly reduce their risk of falling victim to an attack.
In addition to strong passwords and regular updates, businesses should conduct thorough risk assessments to identify potential vulnerabilities within their systems. This proactive approach enables companies to address weaknesses before they can be exploited. Monitoring network traffic and user behavior can also help detect unusual activity that may indicate a security breach.

Having a comprehensive incident response plan is equally crucial. This plan should outline the steps to take in the event of a cyber incident, detailing roles and responsibilities, communication strategies, and recovery procedures. A well-prepared response can minimize damage and ensure a swift recovery, allowing the business to bounce back more effectively.
How iTRINITY Consulting Can Help
iTRINITY Consulting specializes in cybersecurity solutions tailored to the needs of South African businesses. We conduct risk assessments to identify vulnerabilities and implement robust security measures, such as firewalls and intrusion detection systems. Additionally, we provide managed security services to monitor your systems around the clock, ensuring your data and infrastructure remain secure against evolving cyber threats.

