iTRINITY Blog
IT Talk
Cybercrime Costs – Financial Losses
It's important to consider that the impact of cybercrime extends beyond direct financial losses. There are also intangible costs such as loss of customer trust, reputational damage, and potential legal consequences, which are not easily...
The Exorbitant Actual Cost of Cybercrime
The Exorbitant Actual Cost of Cybercrime According to the Cybersecurity Ventures, the global cost of cybercrime is projected to reach USD 6 trillion annually by 2021, up from USD 3 trillion in 2015. This includes direct financial losses, as...
Masquerade Attack – Identity Theft
Identity theft is a type of fraud where someone steals another person's personal information, such as their name, identity number, or credit card details, in order to commit financial or other fraudulent activities. Identity thieves can use this...
What Is Malware?
Malware is invasive software or computer code designed to infect, damage, or gain access to computer systems. Some strains of malware target financial data and other sensitive information, and they’re used to commit extortion, fraud, and...
No Fiasco, when you have Cisco
No Fiasco, when you have Cisco Cisco is a multinational technology company based in San Jose, California, United States. Cisco is an acronym that stands for "Computer Information System Company." The company was initially named "Cisco...
What is Phishing?
What is Phishing? Phishing is a type of cyber attack where the attacker uses fraudulent emails or websites to impersonate a legitimate company in order to acquire personal information, such as passwords, credit card numbers, or bank...
With your data in the cloud, you can rest assured!
With your data in the cloud, you can rest assured! Cloud solutions refer to the delivery of computing services, including storage, databases, software, and networking, over the internet. Rather than relying on local servers or personal...
Your 1-stop IT-solution
Your 1-stop IT-solution An IT (Information Technology) solution refers to a comprehensive approach or set of technologies, tools, and services designed to address specific business needs or problems related to information technology. It...
Microsoft Office 365 (O365) – will it work for me?
Microsoft Office 365 (O365) - will it work for me? Factors to consider : Software Requirements Ensure that your devices meet the minimum system requirements for Office 365. Check the supported operating systems, processor specifications,...
Alert! Are you protected against data breaches and malicious activities?
Alert! Are you protected against data breaches and malicious activities? What is a firewall? A firewall is a security device or software application that acts as a barrier between a trusted internal network and an untrusted external network,...
CYBER SECURITY :- to be safe from CYBERCRIME
CYBER SECURITY : to be safe from CYBERCRIME What is Cybercrime? Cybercrime is a form of criminal activity involving the use of computers, networks and the internet. Cybercrime encompasses a wide range of activities, including computer...
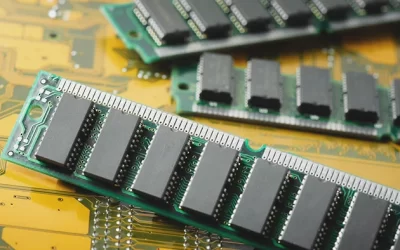
What Is RAM and Why Is It Important?
What Is RAM and Why Is It Important? RAM (random access memory) is one of the most fundamental elements of computing. Every computing device has RAM, whether it is a desktop computer, tablet, smartphone or a smart TV. It is a...
Start with a free IT assessment
A quick assessment of your current IT set up will let us know exactly how and where you can save time and money.
As a well established company, iTRINITY is highly focused on dedicated services, such as Managed IT Services, Cloud Solutions, Hardware & Software, Upgrades, IT Management & Project Management (IT), Solution Design, Networking, Microsoft House, Insurance Assessments, Security, and IT Audits.
Whatever you need in IT, we're here to assist.